Tips to Protect Yourself from Social Engineering Attacks
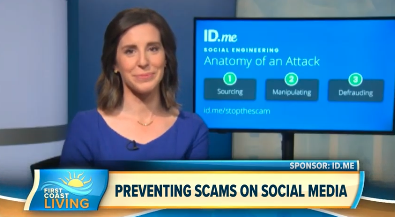
ID.me privacy advocate Mere Work discusses ways to safeguard against social engineering attacks.
Online identity theft is as old as the internet itself. As criminals become more sophisticated, even users who are typically comfortable navigating the internet safely are at risk. ID.me is on the forefront of this fight against fraudsters; over the last year we’ve observed social engineering quickly become one of the most potent scam methods used by cyber crooks.
Social engineering attacks include deceptive practices used to manipulate people with the intent of causing them to divulge confidential information to use for fraudulent purposes.
There are several ways people can spot a scam and protect themselves:
- Proofread for typos in website and email addresses.
Take a closer look at online communications, especially with new people or companies you have not independently verified, and keep your eye out for odd-looking links and typos. - If it seems too good to be true, it probably is.People don’t just give away lottery or other winnings to others they don’t know.
- Beware of unusual messages from friends.
If a friend suddenly reaches out online with bizarre requests or financial offers, it may be a scammer impersonating your friend. - Internet “friends” may not be friends.
Be cautious of any personal connections made online, particularly if you haven’t video chatted or met the person and they ask for money or personal information. - Take a pause on urgent requests.
Scams often rely on creating a sense of urgency with the victim, increasing the likelihood that they will overlook red flags. - Turn your social media profiles private.Attackers use these profiles to learn things about you. Also be suspicious of new social media contacts.
Cybercriminals are increasingly targeting job-hunters. Here are a few tips to stay safe while applying for a new position:
- Confirm postings directly with the hiring company.
Make sure you are visiting the official company website and access job postings directly on the official website of the hiring company. Rather than follow directions from a new contact, reach out to the company directly to verify the request. - Don’t trust a text-message only process.
Be wary of any interview where you aren’t speaking to a representative of the company over the phone, on a video chat, or in-person. Most scams are conducted over text or messenger services to conceal the scammers identity. - Do your homework on company contacts.
Research the company. Look up the individuals you speak with — search their names and use LinkedIn to find their profiles. If the person does not seem to exist or has very few followers, be suspicious of a potential scammer.Ask thoughtful questions that call for answers beyond publicly available info — scammers do their research too.Make sure the hiring manager’s email address is from the official domain of the company — it should not be from a personal address.