500,000 Stolen Logins, Zero Known Breaches: What Happened When Credential Stuffing Hit Two Retirement Systems
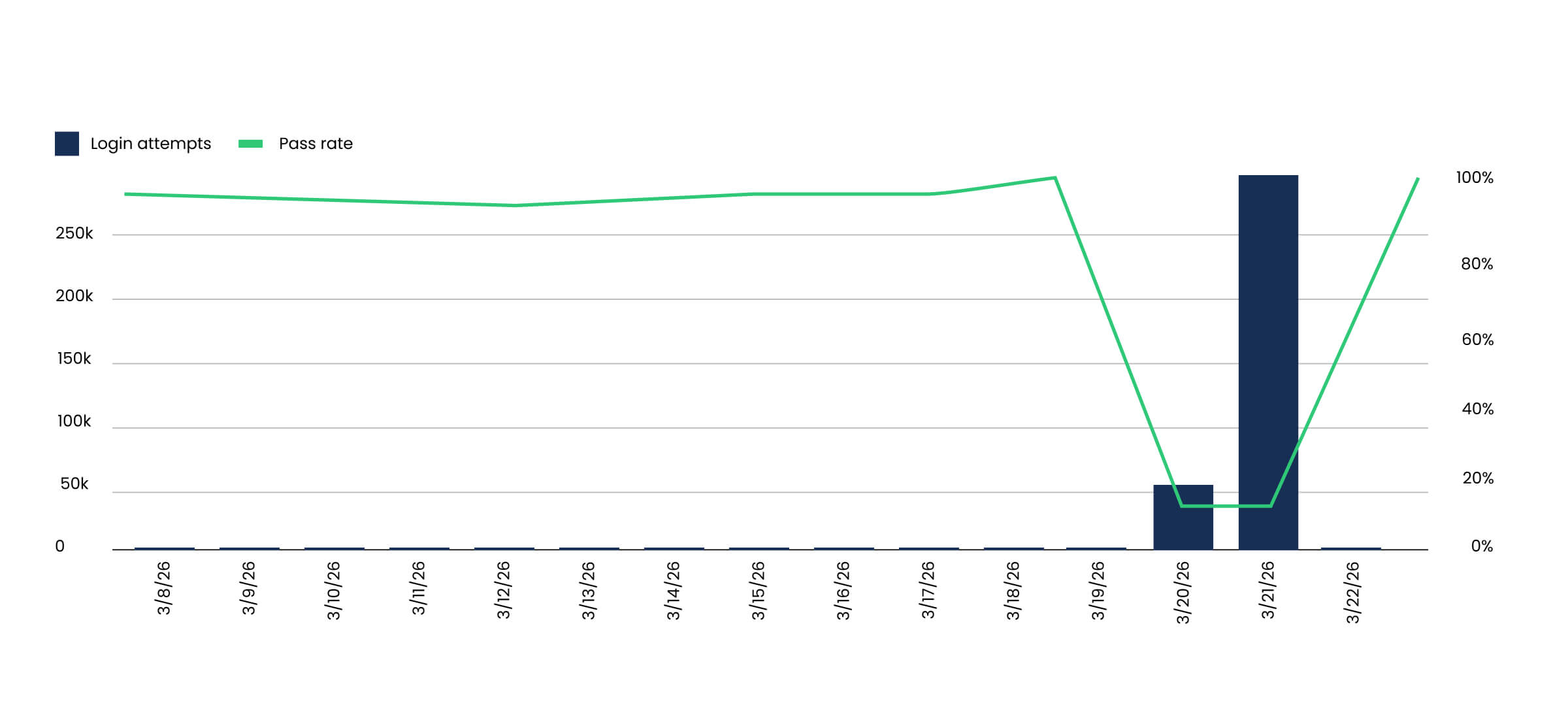
One Friday in March, a state retirement system that typically processes about 200 member login attempts per day saw that number jump to over 200,000. By that Saturday, a second retirement system went from roughly 500 daily login attempts to more than 300,000.
Both agencies were under a credential stuffing attack. Attackers were using stolen username and password combinations harvested from previous data breaches, running them against member login portals at massive scale. Both agencies had identity verification integrated into authentication at the front door. The result: zero known member accounts were compromised, no internal systems were affected, and no staff had to be mobilized over the weekend.
This is a story about where identity is handled, and why that architectural decision changes everything.
Why Retirement Systems Are a Growing Target
Credential stuffing is not new. What is new is where the attacks are landing. There are more than 5,000 public sector retirement systems across the U.S., managing roughly $6 trillion in assets and serving tens of millions of active members and retirees. These portals hold some of the most sensitive financial data in state government: benefit disbursements, banking information, tax records, and personally identifiable information for hundreds of thousands of members. For attackers working through stolen credential databases, these portals are high-value targets.
The attack pattern is also shifting. Attackers are doing reconnaissance across government portals, testing which ones are vulnerable, and rotating targets when they hit a wall. When one agency blocks them, they pivot to the next. Security teams describe it as a “whack-a-mole” problem: the attacks don’t stop, they just move.
This matters for retirement systems in particular because many are in the middle of modernization. Agencies that have historically relied on in-person service and paper-based processes are building digital member portals for the first time. That shift is necessary, but it also opens a new surface for exactly these kinds of attacks.
What Credential Stuffing Actually Looks Like
When a data breach happens, stolen usernames and passwords end up in massive databases that are sold and traded online. Attackers take those credential lists and use automated tools to run them against login pages across the internet, betting that people reuse passwords. They’re often right.
The attack against these two retirement systems followed this exact pattern. Hundreds of thousands of stolen credential pairs were run against the member login portals over two days. The attackers weren’t trying to hack the systems themselves. They were trying the front door with stolen keys, at scale.
The difference between a credential stuffing attack being a nuisance and a crisis comes down to one question: what happens when someone tries a stolen password at your login?
Front Door vs. In-Flow: Where You Verify Changes Everything
Most fraud detection tools sit deeper in the application flow. They monitor for suspicious behavior after a user has already authenticated: unusual transaction patterns, session anomalies, impossible travel. These tools are valuable, but they only help after the attacker is already inside. It’s the equivalent of relying on motion sensors inside a building without securing the point of entry.
Identity verification at the login flips this model. Instead of detecting fraud after entry, it prevents unauthorized access in the first place. When identity is verified at the point of authentication, stolen credentials alone aren’t enough. The system confirms the person, not just a password.
That’s what happened here. The two retirement systems had identity verification at the front door. When 500,000+ stolen credentials were thrown at their portals, the verification layer absorbed the entire attack. The attack was absorbed before it could impact downstream systems. Their security teams didn’t have to respond. Their members were never at risk. The attack never became an incident.
Now consider the alternative. If 500,000 login attempts hit an unprotected portal, even a small success rate creates real consequences. What would your downstream costs look like if even 1% of those attempts succeeded? How many compromised accounts would your team need to investigate? How many members would need to be notified? What’s the cost of resetting credentials, reversing unauthorized transactions, and rebuilding trust with affected retirees? For most agencies, the operational cost of triaging that volume of suspicious activity is significant, even before accounting for financial losses or reputational damage.
That math is the core argument for moving identity to the front of the experience.
What This Means for Agencies Going Digital
Retirement and pension system leaders across the country are currently evaluating how to secure digital member access. Many are watching early deployments closely, and weekends like this one are exactly the kind of real-world test that shapes procurement decisions.
For agencies that already have digital member portals, this is a concrete reminder that credential stuffing is an active, ongoing threat. The question isn’t whether your portal will be targeted. It’s whether the attack will be stopped before it reaches your systems, or whether your team will spend a weekend triaging it.
For agencies building or planning to launch digital portals, this is the case for handling identity at the front of the experience whether in new systems or by integrating it into existing ones. Retrofitting fraud defenses after launch is more expensive, more complex, and leaves a window of exposure during the transition.
The Bottom Line
Two retirement systems were attacked that weekend with over 500,000 stolen login attempts. Both had identity verification at the front door. Neither had a single member account compromised. Neither had to mobilize a response team. Neither incurred any additional cost.
That’s what it looks like when identity is handled as a foundational layer, not an afterthought. If your agency manages a member portal or is planning to build one, see how ID.me secures the front door for state retirement systems.
Mitch Melis is the Public Sector Field CTO at ID.me, where he advises government leaders on digital identity strategy and modern service delivery. He previously served as Commissioner of the Virginia Employment Commission and Director of the Virginia Department of Professional and Occupational Regulation.



